OPNsense 20.1, codenamed “Keen Kingfish”, has been released and brings numerous innovations to the popular open-source firewall.
Key New Features
FreeBSD 11.3 as the Base
OPNsense 20.1 is based on FreeBSD 11.3, which brings updated drivers and security patches. Stability and hardware compatibility have been further improved as a result.
Firmware Updates
The firmware update system has been fundamentally redesigned:
- Changelog view directly in the web interface
- Improved update logic with integrity verification
- Faster update processes
- Better error handling for interrupted updates
DHCPv6 Improvements
- New DHCPv6 client with improved functionality
- Better support for Prefix Delegation
- Optimized IPv6 configuration
- More stable connection recovery
Firewall Improvements
- Extended alias types including GeoIP support
- Improved live log with extended filtering options
- Optimized rule processing
- Improved floating rules
Intrusion Detection
The Intrusion Detection System has been updated:
- Updated Suricata version
- Improved rulesets
- Optimized performance for packet analysis
- Extended alert management
WireGuard
- Improved WireGuard integration as a plugin
- Easier configuration via the web interface
- Better peer management
- Status monitoring for WireGuard tunnels
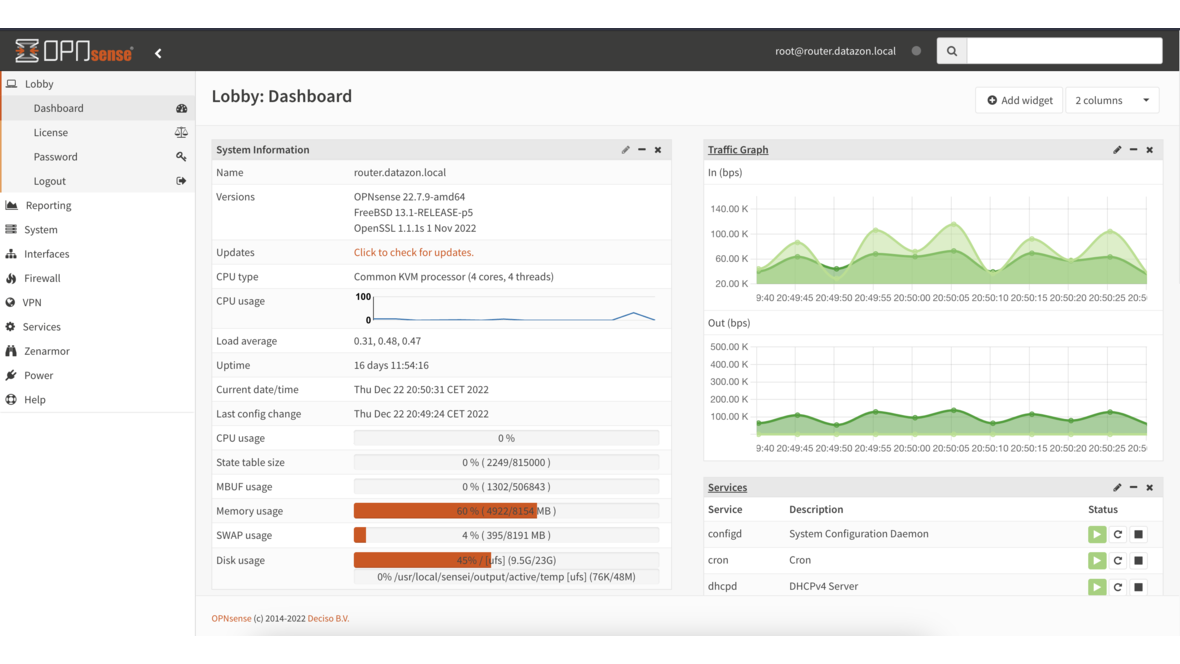
Web Interface
- Modernized dashboard design
- Faster page loading times
- Improved service status
- Extended diagnostics tools
Migration from 19.7
The upgrade from OPNsense 19.7 to 20.1 can be performed directly via the web interface. A backup of the configuration before the upgrade is recommended.
Conclusion
OPNsense 20.1 continues the ongoing development of the platform. The improved DHCPv6 support and WireGuard integration in particular make the update attractive for enterprise use. We are happy to support you with planning and implementing your OPNsense firewall infrastructure.
More on these topics:
More articles
Backup Strategy for SMBs: Proxmox PBS + TrueNAS as a Reliable Backup Solution
Backup strategy for SMBs with Proxmox PBS and TrueNAS: implement the 3-2-1 rule, PBS as primary backup target, TrueNAS replication as offsite copy, retention policies, and automated restore tests.
OPNsense Suricata Custom Rules: Write and Optimize Your Own IDS/IPS Signatures
Suricata custom rules on OPNsense: rule syntax, custom signatures for internal services, performance tuning, suppress lists, and EVE JSON logging.
Systemd Security: Hardening and Securing Linux Services
Systemd security hardening: unit hardening with ProtectSystem, PrivateTmp, NoNewPrivileges, CapabilityBoundingSet, systemd-analyze security, sandboxing, resource limits, and creating custom timers.