A firewall with packet filter rules allows or blocks connections — but it doesn’t detect attacks within allowed connections. An SQL injection attack over port 443, an exploit in an HTTP request, or malware communication over encrypted DNS passes through the packet filter unnoticed. This is where Suricata comes in: as an Intrusion Detection System (IDS), it analyses network traffic in real-time and identifies known attack patterns. In IPS mode (Intrusion Prevention), it blocks them automatically.
What Is Suricata?
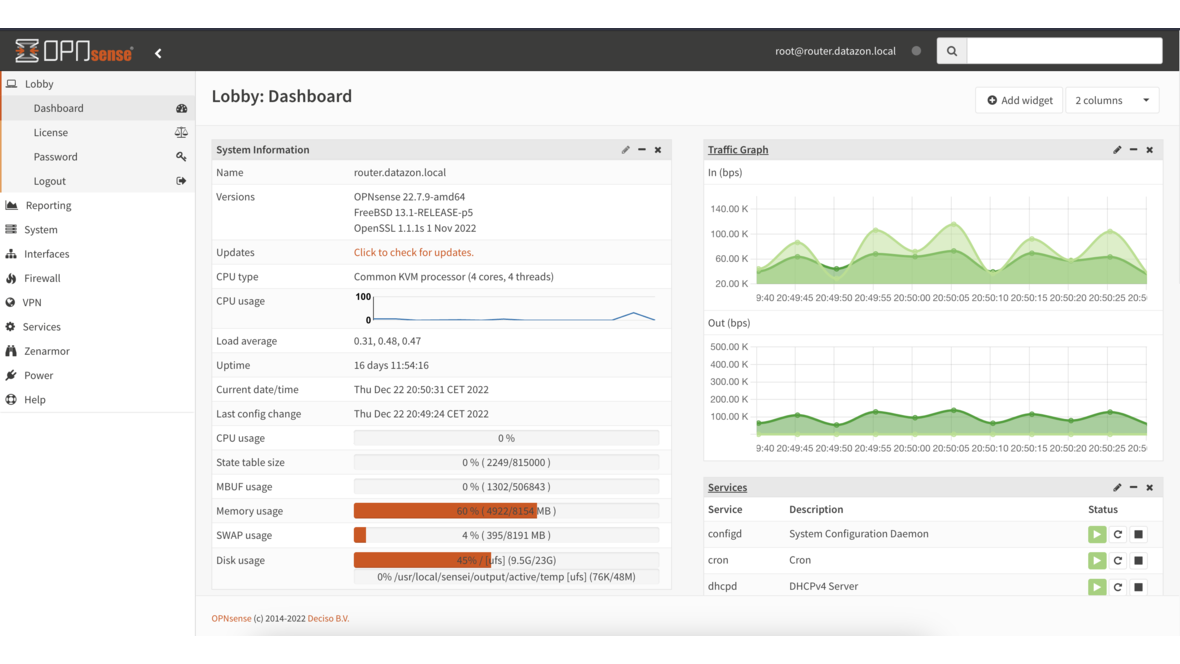
Suricata is an open-source engine for network analysis and threat detection. It analyses network traffic using signatures (rules) that describe known attack patterns. Suricata is natively integrated into OPNsense and can be configured through the web interface.
IDS vs IPS:
- IDS (Detection): Detects attacks and logs them — but doesn’t intervene. Suitable for observation and learning.
- IPS (Prevention): Detects attacks and automatically blocks the associated traffic. Production use after IDS testing phase.
Setup on OPNsense
Step 1: Enable Suricata
Services → Intrusion Detection → Administration:
- Enabled: Activate
- IPS Mode: Initially “IDS” for the testing phase, later switch to “IPS”
- Pattern Matcher: “Hyperscan” (recommended — significantly faster than “Aho-Corasick”)
- Interfaces: Select WAN (and additional interfaces as needed)
- Home Networks: Define internal networks (e.g., 10.0.0.0/8, 192.168.0.0/16)
Step 2: Download Rulesets
OPNsense offers various rule sources:
| Ruleset | Content | License |
|---|---|---|
| ET Open | Emerging Threats community rules | Free |
| ET Pro | Extended Emerging Threats | Commercial |
| Abuse.ch | Malware/botnet-specific rules | Free |
| OPNsense AppDetect | Application detection | Free |
Recommendation: ET Open as the baseline — covers the most important threats and is updated daily. For businesses with elevated security requirements, ET Pro supplements additional signatures.
Services → Intrusion Detection → Download:
- Enable desired rulesets
- Click “Download & Update Rules”
- Set up automatic updates (daily recommended)
Step 3: Configure Rule Categories
Not all rule categories are relevant for every network. A sensible selection:
Enable (recommended):
emerging-malware— Malware communicationemerging-trojan— Trojan activityemerging-exploit— Exploit attemptsemerging-dos— Denial of serviceemerging-scan— Port scans and reconnaissanceemerging-web_server— Web server attacksemerging-sql— SQL injectionemerging-worm— Worm activityemerging-botcc— Botnet C2 communicationemerging-compromised— Known compromised hosts
Optional (context-dependent):
emerging-policy— Policy violations (e.g., Tor usage, P2P)emerging-dns— DNS-based attacksemerging-voip— VoIP-specific attacks
Leave disabled (high false positive rate):
emerging-games— Gaming trafficemerging-chat— Chat protocolsemerging-info— Information gathering (too broad)
Step 4: IDS Testing Phase
Before switching to IPS, run in IDS mode for at least 1–2 weeks:
- Monitor alerts under Services → Intrusion Detection → Alerts
- Identify false positives (legitimate traffic detected as an attack)
- Disable or adjust individual rules that cause false positives
- Only switch to IPS after cleanup
Step 5: Switch to IPS
After the testing phase, switch to IPS mode:
- IPS Mode: Enable “IPS”
- Set rules that should block to “Drop” (default: “Alert”)
- Initially set only critical categories to Drop, keep the rest as Alert
Performance Tuning
Suricata can require significant CPU resources, especially at high throughput.
Hardware Sizing
| Network Throughput | Recommended CPU | RAM |
|---|---|---|
| Up to 100 Mbit/s | 2-core (Intel i3/Celeron) | 4 GB |
| Up to 500 Mbit/s | 4-core (Intel i5/Xeon E) | 8 GB |
| Up to 1 Gbit/s | 4–6-core (Intel i5/Xeon) | 16 GB |
| Up to 10 Gbit/s | 8+ core (Xeon/EPYC) | 32 GB |
Optimizations
Enable Hyperscan: Intel’s “Hyperscan” pattern matcher is significantly faster than the default “Aho-Corasick”. Available on all x86 systems.
Disable unnecessary rules: Every active rule costs CPU time. Disable rules irrelevant to your network (e.g., VoIP rules without VoIP infrastructure).
Define Home Networks correctly: Suricata only inspects traffic for defined home networks. Correct definition reduces unnecessary analysis.
Adjust flow memcap: Under high traffic, the default memory limit for flow tracking can be increased:
- Services → Intrusion Detection → Administration → Advanced
- Increase
flow.memcapto 128 MB or 256 MB (default: 64 MB)
Typical Detections
Suricata detects, among others:
Network attacks:
- Port scans (SYN scan, FIN scan, XMAS scan)
- Brute-force attempts (SSH, RDP, FTP)
- DNS tunneling (data exfiltration via DNS)
- ARP spoofing and MITM attempts
Web attacks:
- SQL injection (UNION-based, blind SQLi)
- Cross-site scripting (XSS)
- Directory traversal (../../../etc/passwd)
- Web shell uploads
Malware communication:
- Command-and-control traffic (known C2 domains and IPs)
- Ransomware beacons
- Exploit kit downloads
- Cryptominer traffic
Alert Management
Interpreting Alerts
Each alert contains:
- Severity (1 = critical, 2 = high, 3 = medium)
- Signature ID (SID) — Unique rule number
- Source and destination IP
- Description — What was detected
- Category — Malware, exploit, policy, etc.
Automation
Suricata alerts can be forwarded to external systems via syslog:
- SIEM integration: Send alerts to Graylog, Elasticsearch, or Splunk
- Email notification: OPNsense can send emails for critical alerts
- DATAZONE Control: Aggregate alerts centrally and correlate across all sites
IDS/IPS Combined with Blocklists
Suricata and IP blocklists complement each other:
- Blocklists block traffic at the IP level — fast, efficient, no deep packet inspection needed
- Suricata analyses the content of allowed connections — detects attacks within legitimate traffic
Together, they provide defense-in-depth: blocklists catch known attackers, Suricata identifies new or unknown attack vectors.
Frequently Asked Questions
Does Suricata slow down my internet connection?
In IDS mode: No — Suricata analyses a copy of the traffic. In IPS mode: Minimally — traffic is inspected inline, latency typically increases by <1 ms. With undersized hardware, bottlenecks may occur during peak loads.
How many false positives should I expect?
With ET Open and a sensible rule selection: 5–20 false positives in the first week. After tuning in the IDS phase: 0–2 per week. The testing phase is critical for clean IPS operation.
Can Suricata analyse encrypted traffic (HTTPS)?
Not directly — encrypted traffic is by definition unreadable. However, Suricata can analyse TLS metadata (SNI, JA3 fingerprints, certificates). For full HTTPS inspection, a TLS proxy would need to be placed upstream, which has privacy implications in practice.
Does Suricata replace a firewall?
No. Suricata supplements the packet filter, it doesn’t replace it. The packet filter defines which traffic is fundamentally allowed. Suricata inspects the allowed traffic for attack patterns.
Want to set up IDS/IPS on your OPNsense firewall? Contact us — we configure Suricata and tune the rules for your network.
More on these topics:
More articles
Backup Strategy for SMBs: Proxmox PBS + TrueNAS as a Reliable Backup Solution
Backup strategy for SMBs with Proxmox PBS and TrueNAS: implement the 3-2-1 rule, PBS as primary backup target, TrueNAS replication as offsite copy, retention policies, and automated restore tests.
OPNsense Suricata Custom Rules: Write and Optimize Your Own IDS/IPS Signatures
Suricata custom rules on OPNsense: rule syntax, custom signatures for internal services, performance tuning, suppress lists, and EVE JSON logging.
Systemd Security: Hardening and Securing Linux Services
Systemd security hardening: unit hardening with ProtectSystem, PrivateTmp, NoNewPrivileges, CapabilityBoundingSet, systemd-analyze security, sandboxing, resource limits, and creating custom timers.