With the end-of-life of Sophos UTM, many organizations face the question of which firewall solution to migrate to. OPNsense stands out as a powerful, open-source alternative. In this article, we explain why the switch makes sense and how the migration can be carried out successfully.
Why Move Away from Sophos UTM?
End-of-Life and End of Support
Sophos has announced the end-of-life for the UTM product line. This means:
- No more security updates after the end of support
- No new features or improvements
- Growing security risk in ongoing operations
- Migration to Sophos XGS or an alternative is necessary
Rising Licensing Costs
- Annual license fees for Sophos products continue to increase
- Hardware-bound licenses restrict flexibility
- Module-based licensing makes the full feature set more expensive
Why OPNsense?
Open Source and Free of Charge
- No licensing costs — the software is completely free
- No vendor lock-in
- Transparent source code reviewed by the community
- Commercial support options available
Feature Set
OPNsense offers a feature set that competes with commercial solutions:
- Stateful Firewall with an intuitive rule set
- VPN — WireGuard, OpenVPN, IPsec
- IDS/IPS with Suricata
- Web Proxy with caching and filtering
- DNS Resolver with Unbound (including DNS-over-TLS)
- DHCP Server and relay
- Captive Portal for guest networks
- Traffic Shaping and QoS
- High Availability with CARP
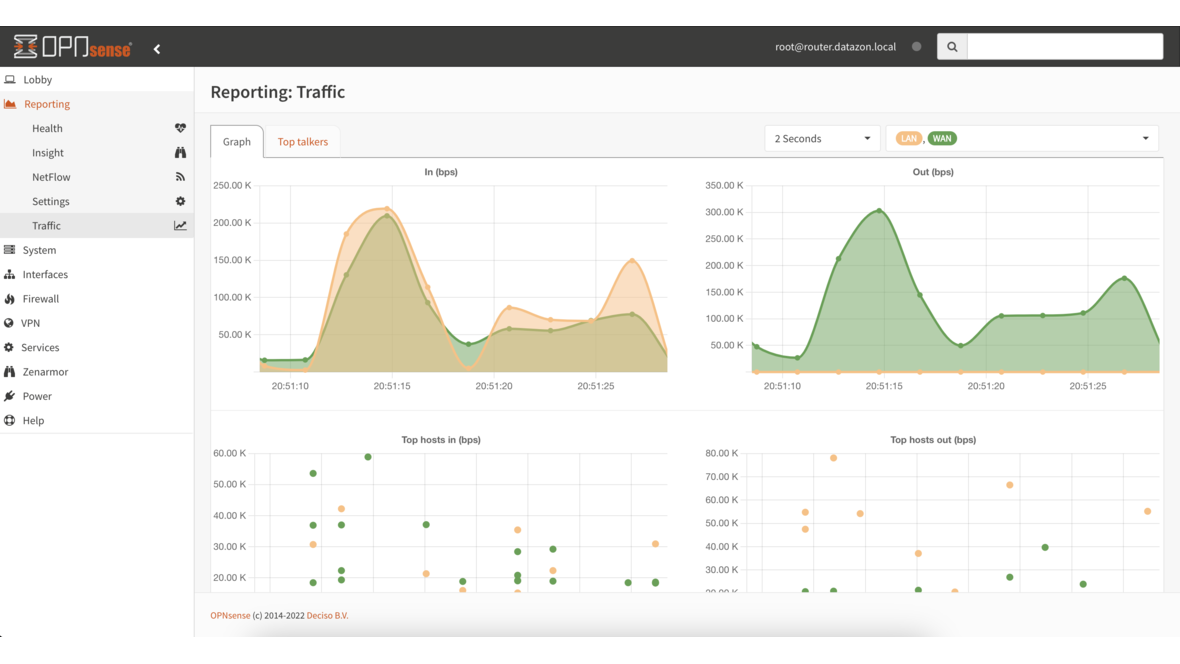
- Reporting and Monitoring
Regular Updates
- Bi-weekly security updates
- Two major releases per year
- Active community and professional support
Migration Planning
Preparation
-
Inventory of the current Sophos UTM configuration
- Document firewall rules
- Record VPN connections
- List NAT rules
- Back up DNS and DHCP configuration
- Document network interfaces and VLANs
-
Hardware Planning
- OPNsense runs on standard x86 hardware
- Sizing depends on throughput and features
- Recommendation: Intel-based systems with AES-NI
- Plan for sufficient network interfaces
-
Test Environment
- Set up a parallel test environment
- Test the configuration in advance
- Validate VPN connections in the lab
Migrating Firewall Rules
Sophos UTM rules cannot be imported directly. The migration is performed manually:
- Network objects — create as OPNsense aliases
- Firewall rules — recreate them — OPNsense uses a different rule logic (first match)
- NAT rules — transfer manually
- Note: OPNsense blocks by default — create rules explicitly
Migrating VPN Connections
- Site-to-Site IPsec — carry over parameters (IKE version, cipher, PSK/certificates)
- OpenVPN — migrate configuration and certificates
- WireGuard — evaluate as a modern alternative to OpenVPN
- Reconfigure SSL VPN clients for the new setup
DNS and DHCP
- DHCP scopes — recreate in OPNsense
- DNS entries — configure in the Unbound DNS resolver
- Transfer static DHCP leases
Comparison: Sophos UTM vs. OPNsense
| Feature | Sophos UTM | OPNsense |
|---|---|---|
| Licensing Costs | Yes (annual) | None |
| Firewall | Yes | Yes |
| IDS/IPS | Yes | Yes (Suricata) |
| VPN (IPsec) | Yes | Yes |
| VPN (WireGuard) | No | Yes |
| Web Application Firewall | Yes | Plugin (NGINX) |
| Email Filtering | Yes | Plugin |
| Web Proxy | Yes | Yes |
| Reporting | Yes | Yes |
| High Availability | Yes | Yes (CARP) |
| API | Limited | Full |
| Open Source | No | Yes |
Tips for a Successful Migration
- Take it step by step — do not migrate everything at once
- Documentation — record all changes
- Backup — back up OPNsense configuration regularly
- Maintenance window — plan enough time for the switchover
- Rollback plan — keep Sophos UTM available as a fallback
- Monitoring — monitor firewall logs intensively after the migration
Conclusion
Migrating from Sophos UTM to OPNsense is a worthwhile step. OPNsense offers a comparable feature set without ongoing licensing costs and benefits from an active community as well as regular updates. As an experienced OPNsense integrator, we support you with the planning and execution of the migration — from inventory assessment to production operation.
More on these topics:
More articles
Backup Strategy for SMBs: Proxmox PBS + TrueNAS as a Reliable Backup Solution
Backup strategy for SMBs with Proxmox PBS and TrueNAS: implement the 3-2-1 rule, PBS as primary backup target, TrueNAS replication as offsite copy, retention policies, and automated restore tests.
OPNsense Suricata Custom Rules: Write and Optimize Your Own IDS/IPS Signatures
Suricata custom rules on OPNsense: rule syntax, custom signatures for internal services, performance tuning, suppress lists, and EVE JSON logging.
Systemd Security: Hardening and Securing Linux Services
Systemd security hardening: unit hardening with ProtectSystem, PrivateTmp, NoNewPrivileges, CapabilityBoundingSet, systemd-analyze security, sandboxing, resource limits, and creating custom timers.